The welcoming remarks delivered at the start of the conference.
Welcome to the first
Critical Code Studies Conference.
I'd like to begin by thanking our hosts: The Center for Transformative Scholarship and the Institute for Multimedia Literacy. Thanks to: Tara, Holly, Stacy, and all the staff who helped make this possible I'd also like to thank: Richard Fliegel, Associate Dean for Undergraduate Programs for the College of Letters, Arts, and Sciences, which allowed the independent study, which Max Feinstein took and made this all happen.
The College of Letters, Arts, and Sciences... Letters, Arts, and Sciences, that about sums up Critical Code Studies. Studying the Art of Using Letters in Science. The Artistic Science of Using Letters. Letters applied to the Art of Science.
Critical Code Studies is the interpretation of the extra-functional significance of computer source code. Extra not in the sense of outside of but growing from.
As many of you know, this Conference is a direct outcome of the Critical Code Studies Working Group held online in the Spring, which featured: over 100 members who worked for 6 weeks, producing over 300 lengthy posts and re-posts in weekly discussions, bibliographic annotations, and threads dedicated to interpretations of individual code objects.
Objects of study ranged from works of:
The last of these inspired at least one article and a multi-authored book-length project to be published by MIT Press: One book out of one line.
There is certainly plenty to talk about in the code. Of course, Humanities folks, and the hybrids gathered here, are good at finding things to talk about at finding meaning.
Topics covered in the working group ranged from: evaluating various types of interpretations to how we should read the code? Using what devices? Issues of gender, race, class, and sexuality arose as well as more language specific questions: concerns of how CCS might apply to procedural, object-oriented, declarative, functional. Languages ranged from Lisp to Haskell, Scheme, C++, Javascript
The weeks were driven by the intriguing and powerful presentations by:
Jeremy Douglass: who asked us to seek code readings in the wild.
Dennis Jertz: who invited us to collaboratively annotate ADVENTURE.
Wendy Chun: Who offered a provocative and rich chapter of her forthcoming manuscript
Stephen Ramsay: Who performed a Live reading of Live Coding in a video available on Vimeo
and
Mez Breeze, who presented one of
her inimitable codeworks that collapse computer and natural language realms.
The six weekly discussion threads from that conference are to appear in electronic book review.
The proceedings from this conference will appear in USC's excellent, dynamic Vectors journal
There are many vectors going out from CCS. As well as vectors coming in. We have over 40 gathered here from as far as the UK and as near as USC. And the papers demonstrate the diversity of approaches that are forming CCS. More recently we have been engaged by members of Computer Science who have asked in online discussion forums what exactly we're up to. They are skeptical of the poststructuralist deconstructive interpretive turn.
They, what an unhelpful "pronoun," especially since some of us are skeptical of that same turn.
Nonetheless, it is to the community of computer scientists that I am going to address these few opening remarks.
Why would anyone want to talk about this code?
Computer Science professors have their work cut out for them. What is to staunch the tide of poorly written, barely readable, underdocumented code built to get the job done and to ensure the continued employment and perpetual hatred of anyone forced to encounter it.
When I show these professors some of the code I wish to interpret, they sometimes say, I can't see why anyone would want to talk about that code.
Well, first they ask what I mean by Interpret. An Interpreter is what you build not what you are. But okay, interpret like English Lit style interpret. But that's for poetry not this foobar code.
I am reminded of my own work, trying to teach writing. Or when English Professors -- or their younger counterparts -- assign the Twilight series in a literary survey. I myself once assigned the Da Vinci Code thinking it a book about code, Florentine Inventers Using Fortran. It turns out not to include source code at all. Now I know why people distrust arts and letters. To some that novel was an abomination, Dan Brown played fast and loose with his history. It's offensive when someone plays games with the material without seeming respect for the subject matter. And worse yet, when people start believing it. Retweeting the ideas to you at a party, drink in hand:
Hey, computer guy, let me tell you what I just read about the annakournikova worm.
That's why I think I've seen the word "dangerous" associated with Critical Code Studies. But my humanities training tells me to pay attention when one community calls an interpretive practice "dangerous."
If you could teach Da Vinci Code, what's to be said of a university courses where someone can study reality TV. Should For Whom the bell Tolls be replaced with So You Think You Can Dance? Except the revolution has already occurred, and it wasn't even Tweeted.
I sometimes distract people in the nearby cubicle by reading code aloud. I do that for the meaning I encounter by verbalizing the literal meaning of the symbols, just as I might say the parts of an equation outline. It's not about code poetry or code as poetry, but bringing to code some of the close reading semiotic tools that are applied to such a concise and condensed form.
Reading the "non-art" object was formalized in the work of Stuart Hall and his cultural scholars who dared to write about the Sony Walkman. It found it legs with the com studies workers who took up film and, gasp, popular television. It began to run once the underrepresented took on the cannons.
So, the Code is not a Shakespearian Sonnet. Good. Neither is Skateboarding. Neither are Narcoballads. Neither is the Biltmore Hotel. But perfection or even aesthetic excellence are not and have never been the requirements for the discovery and production of meaning.
We can analyze everything. And we must.
Yes, but why this code? It is not elegant, beautiful, or novel. Where is the "Syntactic Sugar," to borrow and bend Peter J. Landin's phrase?
Beautiful, perhaps not. But is it significant? I would think so.
[Screen grabs from Geekosystem displayed during the talk]
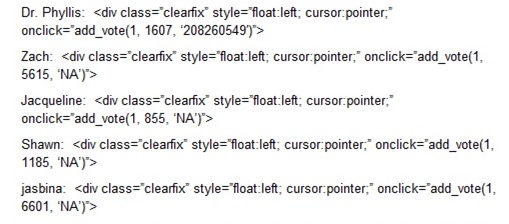
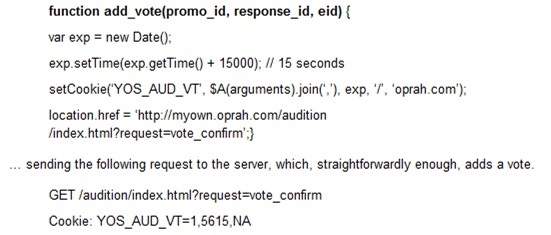
So this code actually comes to us from a website being used in the Oprah Winfrey show where people could vote so someone could be given a hosting position. Here we have the candidates. And you can see the little styling that going on around their names that later gets processed by a function down below.
So that when someone votes for one of these candidates that code gets functioned.
Just to play a little game, "One of these things is not like the others." Which one is it?
The top one --> It doesn't have N/A, it has this crazy number that turns out to be linked to Lilyan Skin Care. The number in the last part of this array are attached to what Geekosystem at first mistakenly interpreted as the Employee Identification Number (EID) but later turns out to be an Entity Identification Number.
When people noticed this particular code they also noticed a certain anomaly. Dr. Phylis seemed to get 2 votes for every one vote that the front runner Zach who had Cerebral Palsy had.
It's not beautiful code, but it is significant.
This is an example of code readings "in the wild." This code was discovered in large part through Geekosystems and also 4chan played a large part in uncovering this mystery of how the voitng system didn't seem to operate quite how the site had described
It's interesting that this number goes to Lilyan Skin care when you think of Oprah Winfrey's show and it relationship to consumer products. That they would mistake Entity ID for Employee ID, when Dr. Phylis seems to be a favorite of the show's website itself, though some have claimed 4chan gamed Zach's early success as well.
Something is curious about this code. It's not well written, it's not well documented, it's not well formatted, they had to re-format this when they published this. It's not reusable, not repurposable, it's not terribly functional.
Before we get to this we should talk about why humanities talk about anything....
But in the span of an hour around or just before 3pm EDT, the woman who had been trailing Anner for some time, Doctor Phyllis, took the lead. And she did so at what sounds to be an unbelievable rate. The Huffington Post reports an increase of 300,000 votes in 20 minutes. Reddit reports 600,000 in an hour. Either way, the voting rates being bandied around are astounding, corroborate with what many Internet denizens who have been
following the proceedings saw, and justly aroused suspicion.At 8pm EDT, another comment appeared on NowPublic that claimed to show the specific difference in the coding. This comment was posted by a
user going by the name b/rother, and it presented the following, reformatted here for easier reading:
The function:
To get there, I must first raise the issue of why humanties scholars talk about anything, because we do tend to talk at length.
I always enjoy going to parties with my wife's colleagues. She's a computer engineer. Unlike parties of English departments where everyone has a ready diatribe on every subject, computer scientists and their cousins, the engineers, actually listen and even remember what you have said. But humanities scholars have lots of opinions, often with a thesis, supported by quotes, framed in pithy packages.
But isn't code for machines?
Programs
must be written for people to read, and only incidentally for machines to
execute. 1 Abelson and Sussman
We are in the business of: reading texts, texts meaning not just printed words, but cultural objects
We have looked at computer games, electronic devices but also hotels, bridges.
We have not just analyzed these objects, we have interpreted them. Said what they mean.
As I have said elsewhere,
Critical Code Studies is the application of hermeneutics to the interpretation of the extra-functional significance of computer source code -- extrafunctional not
meaning outside of function but arising out of and imbricated within, though at times in tension with, function.
So Critical Code Studies examines what code means.
What could that mean? Isn't that what Computer Science does?
At times, yes.
When a computer scientist discusses the relative elegance of one solution over another they highlight an extra-functional aspect of the code.
As Abelson and Sussman write:
A computer language is not just a way of getting a computer to perform/instructions but...a novel medium for expressing ideas about methodology.
But the humanities scholars look for meaning in objects, networks of objects, systems,
They have looked for patterns in the stars and poetry in the moon -- though neither stars nor the moon are their chief area of study.
I focus on interpetation here because the "value" of other humanistic approaches is fairly self-evident:
Historical documentation, for example,
Ah, so is this about metaphors -- about code as metaphors.
my mistress eyes are nothing like Python.
If Perl be her eyes, a messy syntax they
No.
One criticism of my work is that I use the code metaphorically. I have long suspected that weak critical code studies would use code in place of butterflies and waterfalls. In other words, the cultural comment could have little to do with the code itself and would merely use the code to make an unrelated point.
However, when working on my reading of the terrorist database code, ELIZA, or the annakournikova worm, I have come to realize that when I engage in the structures and text of the code, its functioning, and its cultural and historical context, the code itself becomes a way of identifying a cultural phenomenon its structures, its style, its rhetorical approach and that this process is not idle illustration but the very act of interpretation.
In other words, the code-as-metaphor could not be replaced with just any code or any other metaphor. It is not just relevant to the idea being
expressed; it contains the idea.
To use the code metaphorically then is to interpret, and these metaphors are key to expressing my ideas about technoculture. In her article, "The Metaphoric
Circuit: Organic and Technological Communication in the Nineteenth Century," Laura Otis argues for the importance of metaphors even in
scientific writing. She concludes,
[Metaphors] are not simplified translations used to communicate complex or abstract ideas to the public, nor are they decorative rhetorical figures added to engage readers. As can be seen by studying comparisons between organic and technological communications systems, metaphors do not "express" scientists' ideas; they are the ideas. Metaphors suggest new visions, images, and models; they inspire scientists to approach problems in new ways. (1)
The metaphorical examination of code is not a deception; it is not CCS avoiding the code, but CCS interpreting the code.
These are deeply tied tasks....
The future of CCS belongs to Computer Scientists who continue to explore their own code as cultural production and to Humanities scholars who continue to develop their fluency in programming languages and conventions
And perhaps belongs to the dissolution of these categories the convergence of scholarship the re-imagining of a new Liberal Arts that incorporates computation and
interpretation.
Abelson, Harold, Gerald Jay Sussman, and Julie Sussman. Structure and Interpretation of Computer Programs, Second Edition. 2nd ed. McGraw-Hill Science/Engineering/Math, 1996. Print.
Block, Jamie. "Zach Anner Scandal - Oprah Poll Rigged?." Geekosystem 23 June 2010. Web. 25 Jan. 2011.
Marino, Mark C. "Critical Code Studies - Mark C. Marino." electronic book review electropoetics (2006): n. pag. Web. 25 Aug. 2010.
Otis, Laura. "The Metaphoric Circuit: Organic and Technological Communication in the Nineteenth Century." Journal of the History of Ideas 63.1 (2002): 105-128. Print.